Инъекционная косметология, с другой стороны, включает методы, при которых активные вещества вводятся непосредственно в
Бадлон – это уникальный элемент женского гардероба, который сочетает в себе элегантность и практичность.
На протяжении своей карьеры Шварценеггер неоднократно доказывал, что сила воли и трудолюбие могут привести
Долгосрочное употребление алкоголя может привести к необратимым изменениям в организме и трудно поддается лечению.
В нашей статье мы разберем один из видов необходимой мебели для любых салонов красоты,
Подарок в виде браслета для мужчины может быть выразительным жестом, подчеркивающим его стиль, индивидуальность
Это процедура лифтинга, которая базируется на принципе использования радиочастотной энергии для стимуляции коллагена и
Ботокс для волос - это инновационная косметологическая процедура, направленная на глубокое восстановление и укрепление
Миниатюры духов для женщин представляют собой маленькие флакончики ароматов, которые обеспечивают не только удобство
Полуботинки характеризуются низким голенищем, не закрывающим щиколотку, что делает их идеальным выбором для разных
Сумка – это не просто практичный предмет для хранения ваших вещей, но и важный
Женские водолазки - это универсальный и стильный элемент гардероба, который приносит изысканность и комфорт
Компания Arthair Care выделяется на фоне других, предлагая премиальную косметику для волос, которая сочетает
Выбирайте магазин, который предлагает хорошее соотношение цены и качества, и не забывайте об условиях
Массажеры от целлюлита являются одним из популярных и доступных способов борьбы с этим явлением.
Ламинирование ресниц — это современная косметическая процедура, призванная укрепить и улучшить естественные ресницы, придавая
Проведение мероприятий в фотостудии становится все более популярным, благодаря уникальной атмосфере и возможностям, которые
Она основана на использовании лазерного излучения, которое проникает в волосяной фолликул и разрушает его,
Конверсы - это современная обувь, известная своим высоким качеством и продуманными характеристиками.
Фаланговые кольца - это модные украшения для пальцев, которые можно легко купить в интернет-магазинах,
Наращивание волос - это процедура, позволяющая изменить длину, объем, и/или силуэт волос с помощью
Существует огромное количество брендов женской одежды на рынке, представляющих различные стили и ценовые категории.
Первый альбом Армина ван Бюрена "76" был выпущен в 2003 году и сразу получил
Соблюдая правила стирки и сушки изделий из махровой ткани, можно на протяжении нескольких лет
Роскошь королевских домов, невероятной красоты узоры и необычное плетение нитей – вот что такое
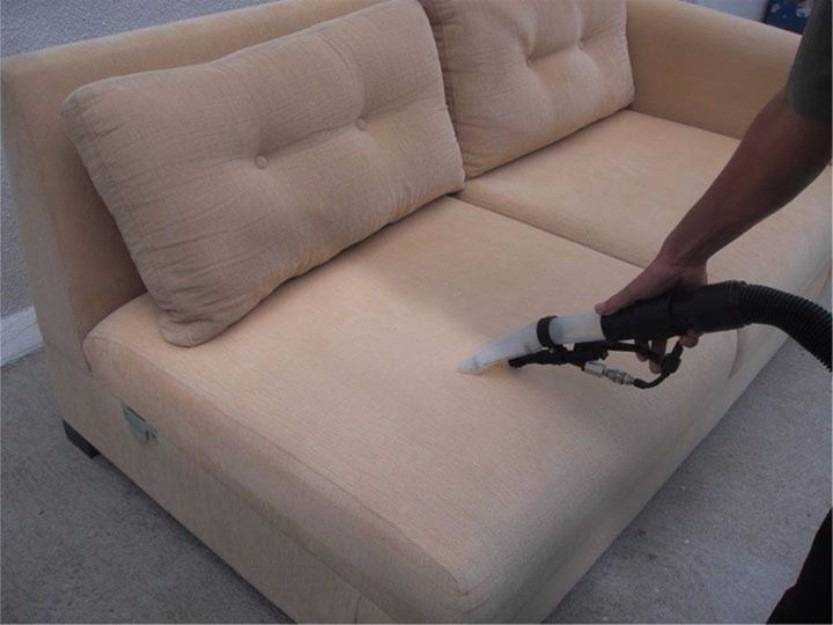
Шенилл — это популярная ткань для обивки мягкой мебели. Она прочная и износостойкая, прекрасно
Виды покрывал и их отличия от накидки. Как выбрать покрывало или сделать своими руками?
Зачем нужно использовать покрывало для дивана? Рекомендации по выбору, виды, формы, размеры накидок, ткани,
Узнайте все о чистке мебели в домашних условиях. Средства для чистки мебели. Способы борьбы